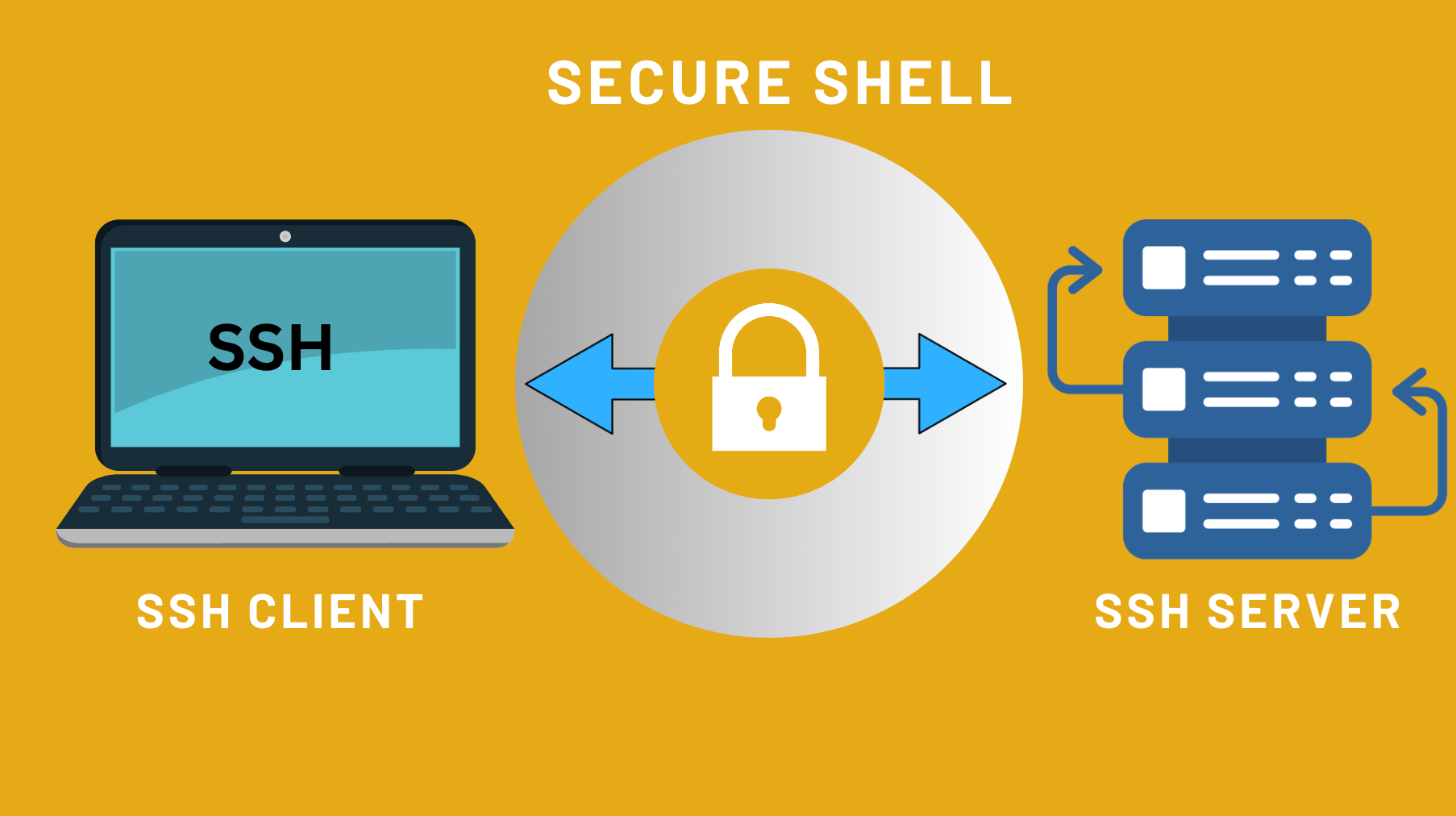
What is Secure Shell?

Secure Shell Protocol simply called SSH is a system with which we can connect to a server remotely for using the command line interface of the server itself. It is securely used for operating network services over an insecure network.
SSH is a very powerful tool yet can be very dangerous if got into the wrong hands. To use SSH, we need an SSH client such as PuTTY for Windows or the default terminal application for mac OS.
The Web Host will give access of Secure Shell to Virtual Private Server and Dedicated Server but not to all Shared Hosting Plans. So, you will need to ask about his to your web host. Some clients rely totally on the web host for managing services and pay them in which case the host will hesitate giving you access to terminal.
Installing an SSH Client on Your Computer:
Before you can use the CLI of your server by Secure Shell, you need to install the correct software for your operating system. The best one for Windows is PuTTY and the built-in terminals will do the work best on you mac OS or Linux machine.
Download Link for PuTTY: https://www.chiark.greenend.org.uk/~sgtatham/putty/latest.html. You can install PuTTY like any other application on Windows easily.
An application named “Terminal” can be run on either UNIX or Linux machine.
Connecting to the Server:
On Windows:
A. For username-password combination:
- Open putty.exe file you just downloaded.
- Type in the host name of your server (Either the primary domain or the IP Address) and click “Open”.
- Type in your username and click “Enter” or “Return”.
- Type in your password and click “Enter” or “Return”.
B. For username-key combination, this might seem like an hassle but it really is not.
- Create a public/private key on your server and download as ppk key.
- Open putty.exe.
- Type the hostname(primary domain or IP Address).
- If you see a “Saved Sessions” box, type a name for this connection and then click “Save”.
- In the menu, click “SSH” and then “Auth”.
- Click “Browse” and select the ppk file you downloaded earlier.
- Click “Connection: and the “Data”.
- Type your username in “Auto-login” username box.
- Click “Session” and save it.
- Now click “Open” and you are good to go.
On UNIX or Linux:
- Open the Terminal.
- Type in ssh username@ip_address.
- If everything goes well, it will prompt your for the password.
Basics of the Command Line:
- cd – change directory
- mkdir – make a new directory
- ls – list files
- vi – view and edit content of a file easily.
Suggested Read: Explore the World of Affiliate Marketing
You can also Contact us on Facebook: https://facebook.com/nestnepalofficial.
Frequently Asked Questions(FAQ)
What is Secure SHell (SHH)?
SSH is a cryptographic network protocol which allows secure remote access to systems and secure file transfers over an unsecured network.
Can I use SSH on different operating system?
Yes, SSH is supported on different Operating System including, Windows, macOS and Linux.
Can SSH be used for file transfers?
Yes, SSH supports secure file transfers through protocols like “Secure Copy” and “SSH File Transfer Protocol” allowing users to securely transfer files between systems.
Are there any Alternatives to SSH for remote access?
While SSH is a popular choice, alternative remote access protocols like Telnet and RDP(Remote Desktop Protocol) exists.
Are there any security risks with SSH?
While SSH is generally secure, risks can arise form weak passwords, Outdated Software and misconfigured settings.
Is SSH widely used in 2023?
Yes, SSH have been used widely in 2023 due to its security, reliability and versatility in managing remote system and secure file transfers.